CAS provides secure log-in experience for many UGA applications
Tuesday, May 26, 2015
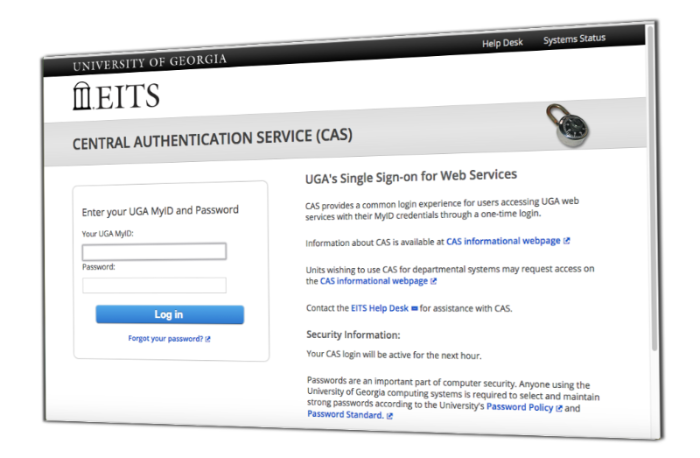
Enter your UGA MyID and password, gain access to a variety of applications, and keep your information secure in the process.
That’s the basic concept behind the Central Authentication Service, or CAS, a single sign-on service used by many applications at the University of Georgia to ensure a secure and consistent log-in process. Athena, the MyUGA Portal and the UGA employee self-service website are just some of the applications that use CAS for user log-ins.
For University students, faculty and staff with MyIDs, CAS provides a uniform experience when accessing these applications.
“It also allows UGA to integrate with third-party sites without sharing UGA passwords, which reduces risk of these services,” said Brian Rivers, associate chief information officer for university information security. Users are also automatically logged out of CAS after 28 minutes or when they close their web browser, which adds another layer of protection.
The single sign-on service is also beneficial to web application developers, as it reduces the exposure of users’ passwords to applications, and it decreases the potential liability that comes with managing and securing passwords.
Before a new web application is authorized to use CAS for its log-in process, it must be vetted by the University’s Office of Information Security, and undergo penetration testing, where the application is intentionally attacked to find security weaknesses.
“We want to provide assurance that there is adequate security in place to protect any information CAS sends to applications and to protect the CAS system from disruption,” said Ben Myers, an associate director of IT in the University’s Office of Information Security.
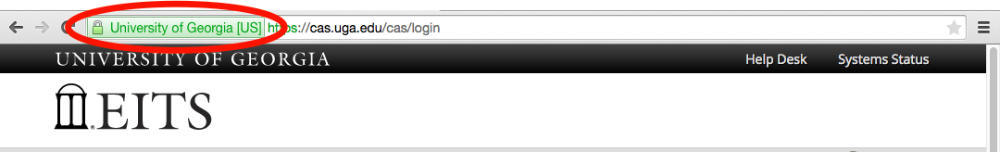
While CAS is a secure way to access many University applications, students, faculty and staff are encouraged to remain vigilant while online. One easy way to stay safe while using CAS? Look for the green lock.
The green lock, located in the left corner of your web browser toolbar before you log into CAS, is an added security measure that lets you know you are interacting with the real CAS site, not a scam or phishing site.
“Not all sites have this feature, but cas.uga.edu does, so don’t log into a CAS page without this lock. Our Security Operations Center team has seen fake CAS pages used in email phishing attacks looking to steal passwords – the fake pages did not display a green lock,” Myers said.
Students, faculty and staff should also be sensitive to situations when they are using CAS on a shared computer, Myers said. In these cases, users should log out of CAS and close the web browser when they are done using a CAS-enabled site. This prevents other users on the computer from being able to hijack the CAS session.
For more assistance with using CAS, contact the EITS Help Desk athelpdesk@uga.edu. For more online security tips, such a choosing a secure password, visit infosec.uga.edu.